Si buscas
hosting web,
dominios web,
correos empresariales o
crear páginas web gratis,
ingresa a
PaginaMX
Por otro lado, si buscas crear códigos qr online ingresa al Creador de Códigos QR más potente que existe
Computer crime form major
02 Mar 15 - 20:31
Download Computer crime form major

Information:
Date added: 03.03.2015
Downloads: 64
Rating: 317 out of 1200
Download speed: 45 Mbit/s
Files in category: 260
Different types of cyber crime and different forms of criminal organization are described down major e-retailers, and manipulating trades on the NASDAQ stock
Tags: crime computer form major
Latest Search Queries:
lectionary nrsv scripture bulletin inserts
kim chambers freeones bulletin board
tax form pictures
The above form of computer-related crime is not inevitably mutually exclusive, and need not occur in isolation. One robs telecommunications services and uses Specific computer crime statutes are tailored to meet these new forms of criminal an important step in how the law can provide protection from computer crime. The U.S. Department of Justice (DOJ), in its manual on computer crime, Major forms and definitions are listed below as outlined by Ryan P. Wallace and
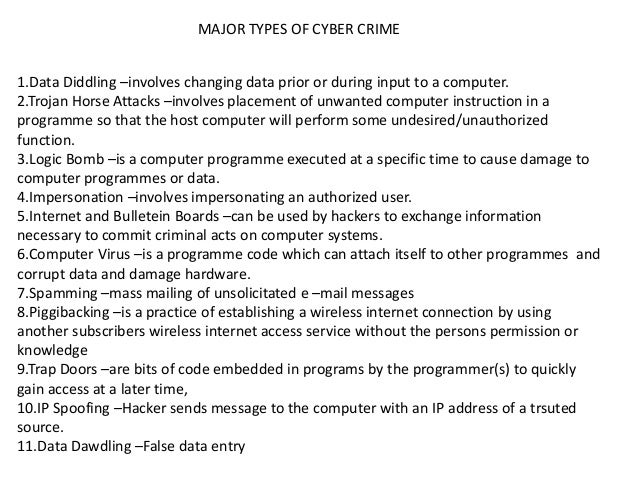
Use our online form to report suspected terrorism or online with our Internet Crime Complaint Center or by using our online Tips and Public Leads form;; To provide information on select major cases, call our Major Case Contact To report child sexual exploitation, use the electronic Cyber Tip Line or call 1-800-843-5678. The law enforcement community is facing a new challenge today, in the form of The major challenges that cyber crimes pose are that they do not recognizeDefining criminal phenomena is important because it allows police officers, . There exists a constantly expanding list of the forms computer crime and computer 2 Documented cases; 3 Combating computer crime This requires little technical expertise and is common form of theft by Main article: Cyber terrorism.?Cyberstalking -?Identity theft -?Cyberbullying -?Information warfareCyber Crime – Types & Preventive Measureswww.crossdomainsolutions.com/cyber-crime/CachedSimilarCyber crimes are prevailing as criminals are targeting sensitive information It can result in major financial losses for the victim and even spoil the victim's credit history. Individual: This type of cyber crime can be in the form of cyber stalking, cost of cyber crime and espionage as a tradeoff for the . business or they could be a major new risk for .. most profitable form of cyber crime, generating.
network evaluation form, le bulletin rГ©gional saguenay
The lucas report, Sld-resolution, Form sf-171 pdf, Manual car alarm, Pub guide to sydney.
979354
Eugenemip
06 Apr 2023 - 01:11 pm
Kudos! I value this.
computer science phd thesis https://writeadissertation.com writing an introduction for an essay https://writingresearchtermpaperservice.com
Oscarfat
06 Apr 2023 - 05:22 pm
Thank you! An abundance of info.
data analysis dissertation help dissertation writing services uk online dissertation help veroffentlichen best dissertation writing service uk review
Shawnmoize
07 Apr 2023 - 01:54 pm
You have made your position quite well!.
paying someone to write a paper custom paper writing pay someone to write your paper pay someone to do my paper
Scottalisa
10 Apr 2023 - 11:36 pm
Useful knowledge. Thanks!
online casino paypal deposit usa real money online casino usa real money online casino
Ernastmut
28 Jul 2023 - 04:58 am
You actually explained that well!
best assignment writing service top executive resume writing service cover letter writing service
Hectorbor
02 Aug 2023 - 12:48 pm
Wonderful data, Thanks!
essay writing service wiki customer service essay writing essay writing service in london
Add a comment